The Seven Deadly Sins of Cyber Security
As an industry leading Managed Service Provider, we have worked and engaged with a large number of organisations across different sectors.

Whilst working closely with businesses, we often see a set of common mistakes being made that put their operations at risk, which we have listed as The Seven Deadly Sins of Cyber Security.
In this blog, we continue review each risk factor and set out to provide a framework of practical steps that businesses can take to better protect themselves from attack.
01. Poor Risk Assessment
There is a genuine misconception amongst many business across the globe that they are not at risk of cyber-attack and that security is not something that they need to prioritise. Many businesses believe that they are not a target due to their scale of business, business function and much more. However, the reality is very different.

Source: Cyber Security Breaches Survey 2020, GOV.UK
According to a sample of businesses and charities surveyed, nearly half of businesses and a quarter of charities had admitted to falling victim of a cyber-attack within the last 12 months and of these businesses and charities, just over 1/3 of businesses and a 1/5 of charities say they experienced these attacks at least once a week. It’s also been reported that these figures have increased quite significantly in both areas since the results have been published.
In some cases businesses that have fallen victim to Cyber-attack have not actually been directly targeted. As many businesses information feature on databases and in some instances are part of a shared community, company details always have the potential to come under attack.
Just over one third of these businesses and one fifth of charities in the same group say they experienced cyberattacks at least once a week.
It is becoming increasingly more important for organizations to identify any vulnerabilities within their network in order to put effective measures in place to mitigate risk which can be done through regular vulnerability assessments. This is a complete scan of an organisations network infrastructure, applications and databases providing more insight of where organisations are most at risk of cyberattack.
02. "Security is a Technology Problem."
The second cyber security sin that we often see is when businesses believe security is a technology problem that can only be remediated with a technology solution. This is something that we see regularly with organisations deploying antivirus or firewall solutions and expecting to capture and counter all cyber security threats. The reality is, that whilst these products are great, they are unable to keep up with the increasing sophistication of such threats, and it’s very common for cyber attackers to exploit companies through human ignorance of how users are vulnerable.

Phishing emails directing people to fraudulent websites are among the most common cyber-attacks on employees. These types of attacks are more common than unauthorised access to networks, making the most frequent (and most targeted) victims of cyber-attacks within organisations their employees. Over the years, cyber attackers have become more sophisticated in their approach, with many phishing emails and fraudulent websites appearing genuine.
When it comes to cyber security, there is a real need to take a holistic approach to the dangers involved and not fall victim to only the marketing of security solutions often claiming to capture and mitigate all of these risks. In order for security solutions to be effective, organisations need to consider people, process and technology in their approach.
Phishing attacks on employees represent one of the most common cyber-attacks.
Businessses need to implement those technology solutions that both protect themselves against risk whilst not impeding staff productivity. The right processes must be firmly in place to ensure that staff know what to do if they suspect a security breach. With employees being so highly targeted, investing in security training, education and awareness of how people can be vulnerable to cyber-attack is critical.
With a wide selection of different IT security solutions available, it is vital that organisations implement the right solution to keep their business, employees and customers safe.
03. Naivety to Security Responsibly
The adoption of cloud based services particularly around email represents a big change in the market. For long periods of times organisations have had a tendency to manage the security within customer environments on site and as email services have started to transition into cloud, there seems to be a lot of naivety around responsibility.
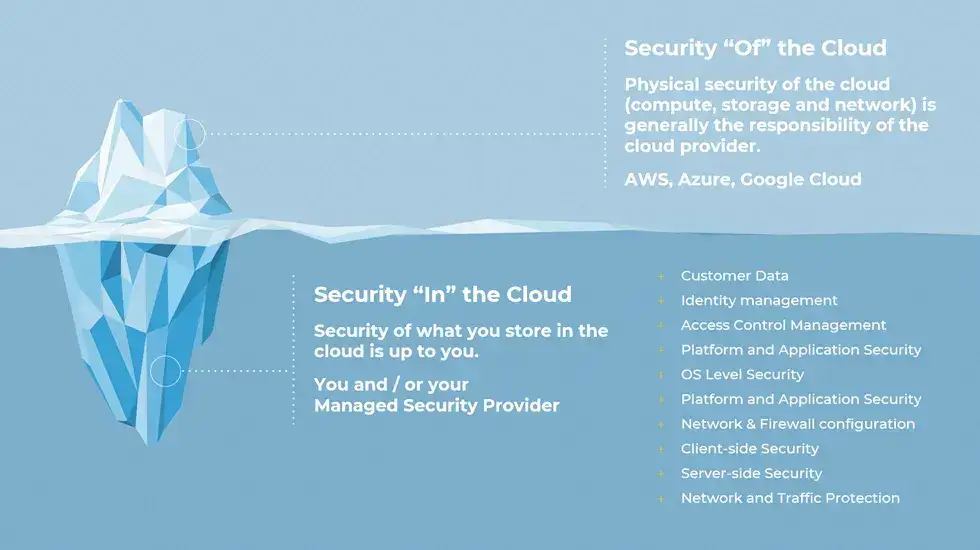
There is often an expectation from organisations that their cloud hosts are fully responsible for the security of their data stored in cloud and that nothing additionally needs to be done to ensure the security of their systems. However, when organisations migrate services into a cloud environment, they need to think carefully and consider what the implications are for the security of these services and need to put the right security measures in place.
Physical security of the cloud is generally the responsibility of the cloud provider, while security of what is stored in the cloud is the responsibility of the organisation or their managed security service provider.
Wanstor’s Integrated Cyber Defence Platform unifies cloud and on-premises security to protect users, information, messaging and the web, powered by unparalleled threat intelligence.
04. Ignoring the Basics
Another cyber security sin that we see is when businesses ignore the basic principles of keeping their network safe. These are the things that fall into the day-to-day administration of businesses IT estate and IT services and these are the foundational things that we regularly see organisations missing each day. As previously mentioned sometimes these will fall under the assumption that some aspects of security are not the organisations responsibility.

We were quite surprised at the number of organisations that still had Windows 2008 servers in operation naïve to the fact that they are no longer supported or updated. A lack of software updates and patching means that organisations are highly vulnerable to exploitation by cyber criminals.
It’s no longer just about securing your network, it’s also about securing the individual endpoint and user.
There are fundamental technologies and best practices such as having Multi-factor Authentication enabled for all users especially in the context of remote working and the increased use of cloud services accessed outside of organisational private network, this becomes extremely important.
Another basic measure organisations can put in place is Password Management. This covers not just training your staff to ensure that their passwords are effective but also putting the organisational policies in place across all applications to ensure that passwords are updated frequently.
05. Neglecting to Audit
A big mistake we see organisations make is failing to audit. An audit is the stage in which organisations find out how impactful their security measures have been which is an essential part of maintaining a secure environment.
Auditing in general is something that IT departments are becoming more familiar with however, it is a relatively new area for many IT teams. To get the most out of an IT audit, it is highly recommended to audit against particular standards such as ISO 27001.
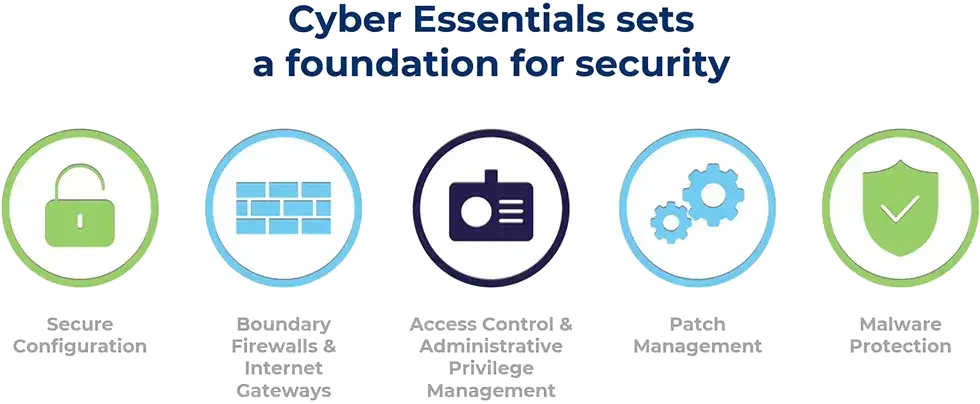
The Cyber Essential Certification is built around five basic technical controls, specifically designed to prevent the most common cyber-attacks, which include malware, ransomware and phishing. Obtaining this standard enables certified organisations to demonstrate and reassure their customers that they are serious about safeguarding the integrity of their data.
06. Don’t lose sight of the reasons
When going through the process of security auditing and implementing security solutions, it is important that organisations don’t lose sight of the reasons why they are putting security measures in place.

Often times organisations fall into the habit of implementing security measures for compliance and auditing purposes which can lead to solutions being put in place that may not necessarily be fit for purpose or most effective.
Organisations must remember that the primary reason for implementing security is to keep their network, employees and customer data safe.
As mentioned earlier in our blog, just over one third of businesses and one fifth of charities in the same group say they experienced cyberattacks at least once a week. The key benefit to implementing a security solution is that if cyber-attacks do occur the impact is likely to be minimal compared to if there wasn’t a security measure in place at all.
07. Not packing your parachute
In the context of IT services, when we talk about not packing your parachute, your parachute is essentially a back-up and disaster recovery plan. It’s very worrying when organisations think that they are not going to ever experience a cyber incident and it’s essential to put in place a proper plan for the inevitable manifestation of an incident within an organisation.

Over the last 3 years we’ve seen several cases where customers have had encryption of their data by malicious code. When that happens the recovery process involves either paying a ransom or restoring from back-up and it’s usually at that moment that organisations heavily rely on the presence of a solid regime of back-up recovery.
It doesn’t necessarily need to be a malware incident that leads organisations to relying on back-up. It could be patch that goes wrong or any other form of update that doesn’t go to plan. A real solid culture of planning and practicing the processes of backing up data and restoring data is a fundamental aspect of managing the cyber risks within organisations.
It’s really important also when thinking about back-up and recovery to make sure that the process is aligned to the business requirements and is discussed with senior management. Often times we see decisions being made at an IT level without the involvement of senior management which can result in a conflict of expectation when it comes to the recovery process.
To find out more about how we could help you identify and mitigate risk across your entire network, click here to get in touch with one of our cyber security experts.
