Seven Steps to a Successful WiFi Site Survey
When undertaking a Wi-Fi survey, there are many different considerations to put into place to ensure that it is as successful as possible. But firstly, what is a wireless site survey?
What is a wifi site survey?
When most people are asked to define a wireless survey the response most often is to determine RF coverage. In the early days this definition was correct however with present day wireless networks there is also a need to provide for higher density environments. To achieve this the survey must now encompass much more than just coverage, we are looking for potential sources of interference as well as proper placement, installation and configuration of 802.11 devices.
Step 1: Determine the need for a site survey
It is absolutely essential to perform a site survey when implementing or refreshing your Wireless LAN. From small to large businesses, performing the survey and asking question of the customer will help determine the objectives, requirements and goals of the WLAN. Different businesses have different requirements and WLAN concerns that will be unique on a customer by customer basis.
Asking the correct questions will assist in a design that meets the coverage and capacity needs.
Step 2: Agree Special Access
From security clearances and wayleaves, to acquiring the appropriate protective clothing, there are various precautions to undertake in the assurance of a safe and successful WiFi site survey. In doing this, it will enable you to undertake a Wi-Fi survey while following all appropriate safety and legality measures.
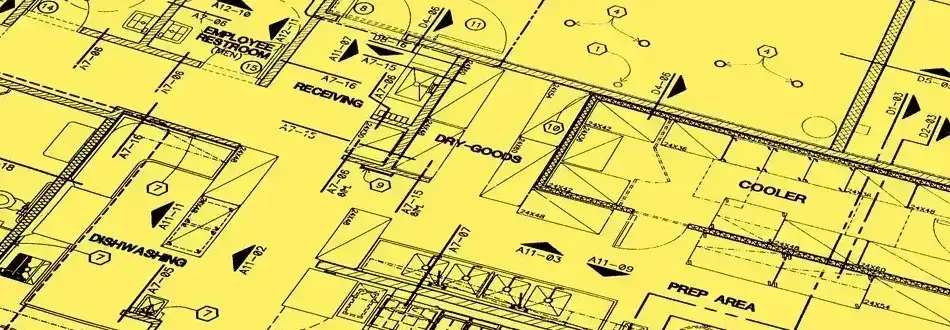
Step 3: Obtain Floorplans
To undertake a Wi-Fi site survey, knowing the location and the scope of the project is essential. This is done by reviewing all previously existing equipment and access points while analysing the existing Wi-Fi infrastructure.
Step 4: Identify what access points are required
The survey will allow you to identify the best location for your access points and orientation of the antennas. This allows you to correctly cover the entire perimeter ensuring maximum performance and coverage of the wireless network. The AP models and types will be determined as part of the design process.
You’ll receive a full Wi-Fi survey report, which will thoroughly outline any work required to maximise your network coverage
Step 5: Infrastructure Connectivity
If it’s a pre-existing wired-network infrastructure, part of the survey will determine how the APs are to integrate into the existing wired architecture.
For new requirements a data cabling company can provide you with more specifics on how long an installation can take, since every job is unique and specific to your requirements and location.
Step 6: Design and installation
Our engineers can design your network to overcome any previously identified issues within the Wi-Fi survey. We’ll look at all aspects of your building and network design, checking the type of internet connection currently used at your site. You’ll receive a full Wi-Fi survey report, which will thoroughly outline any work required to maximise your network coverage.
Step 7: Test
The final stage of your wireless survey will involve a test. This will include diagnosing any issues within your existing network as well as an inspection and test of your existing infrastructure to ensure it is fit for purpose and scalable for your business requirements.
Our WiFi survey expert consultants will visit your business with a variety of mobile testing equipment and software to measure and analyse your WiFi environment. This will involve looking at the many different factors that could affect your network performance using our WiFi site survey software.
To find out more about how our WiFi Site Survey can help you, please get in touch with us.
